What is Spyware? Spyware is unwanted software, a type of malicious software or malware, designed to expose sensitive information, steal…
Cryptography Latest 2022
What is Cryptography? Cryptography is the practice of securing and transmitting data and information in a form that only authorized…
Encryption Latest 2022
What is Encryption? Encryption -In cryptography, encryption is the process of encoding information or sensitive data so only authorized parties…
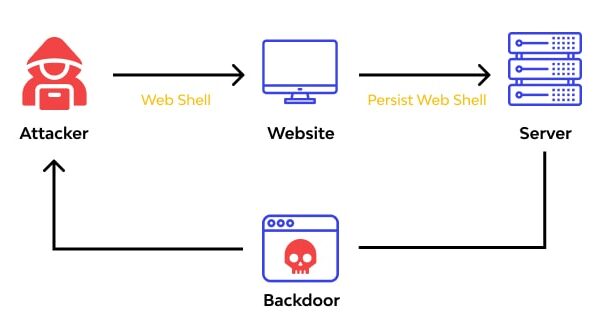
Web Shell Attacks 2022
What are Web Shell Attacks? How to Protect Your Web Servers Web Shell Attacks -During a web shell attack, a…
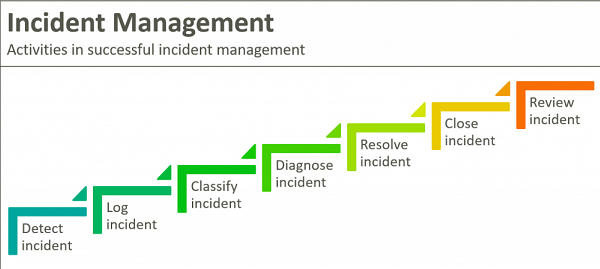
Incident Management 2022
What is Incident Management? Incident Management restores normal service operation while minimizing impact to business operations and maintaining quality.An incident,…
Firewall Threats and Vulnerabilities Latest 2022
What is Firewall Threats and Vulnerabilities ? Firewalls are a basic part of any company’s cybersecurity architecture. However, firewalls alone…
Patching Latest 2022
What does patching mean in it? Patching is a process to repair a vulnerability or a flaw that is identified…
GRC Latest 2022
What is GRC? GRC is the integrated collection of capabilities that enable an organization to reliably achieve objectives, address uncertainty…
CCPA Latest 2022
What is the CCPA (California Consumer Privacy Act )? California Consumer Privacy Act or AB 375 is a new law…
CrPC Sec 439 High Court Decision Latest
If accused appears before trial after receiving notice from PS for filing chargesheet, his bail plea under CrPC Sec 439…