Penetration Testing Latest 2022
What is penetration testing ?
A penetration testing, also known as a pen test, is a simulated cyber attack against your computer system to check for exploitable vulnerabilities. In the context of web application security, penetration testing is commonly used to augment a web application firewall (WAF).
Penetration testing can involve the attempted breaching of any number of application systems, (e.g., application protocol interfaces (APIs), frontend/backend servers) to uncover vulnerabilities, such as unsanitized inputs that are susceptible to code injection attacks.
Insights provided by the penetration test can be used to fine-tune your WAF security policies and patch detected vulnerabilities.
A penetration test (pen test) is an authorized simulated attack performed on a computer system to evaluate its security. Penetration testers use the same tools, techniques, and processes as attackers to find and demonstrate the business impacts of weaknesses in a system.
Penetration tests usually simulate a variety of attacks that could threaten a business. They can examine whether a system is robust enough to withstand attacks from authenticated and unauthenticated positions, as well as a range of system roles. With the right scope, a pen test can dive into any aspect of a system.
What are the benefits of penetration testing?
Ideally, software and systems were designed from the start with the aim of eliminating dangerous security flaws. A pen test provides insight into how well that aim was achieved. Pen testing can help an organization
1-Find weaknesses in systems
2-Determine the robustness of controls
3-Support compliance with data privacy and security regulations (e.g., PCI DSS, HIPAA, GDPR)
4-Provide qualitative and quantitative examples of current security posture and budget priorities for management
Penetration testing stages
The pen testing process can be broken down into five stages.
1-Planning and reconnaissance
The first stage involves:
Defining the scope and goals of a test, including the systems to be addressed and the testing methods to be used.
Gathering intelligence (e.g., network and domain names, mail server) to better understand how a target works and its potential vulnerabilities.
2-Scanning
The next step is to understand how the target application will respond to various intrusion attempts. This is typically done using:
- Static analysis – Inspecting an application’s code to estimate the way it behaves while running. These tools can scan the entirety of the code in a single pass.
- Dynamic analysis – Inspecting an application’s code in a running state. This is a more practical way of scanning, as it provides a real-time view into an application’s performance.
3-Gaining Access
This stage uses web application attacks, such as cross-site scripting, SQL injection and backdoors, to uncover a target’s vulnerabilities. Testers then try and exploit these vulnerabilities, typically by escalating privileges, stealing data, intercepting traffic, etc., to understand the damage they can cause.
4-Maintaining access
The goal of this stage is to see if the vulnerability can be used to achieve a persistent presence in the exploited system— long enough for a bad actor to gain in-depth access. The idea is to imitate advanced persistent threats, which often remain in a system for months in order to steal an organization’s most sensitive data.
5-Analysis
The results of the penetration test are then compiled into a report detailing:
Specific vulnerabilities that were exploited
Sensitive data that was accessed
The amount of time the pen tester was able to remain in the system undetected
This information is analyzed by security personnel to help configure an enterprise’s WAF settings and other application security solutions to patch vulnerabilities and protect against future attacks.
Penetration testing methods
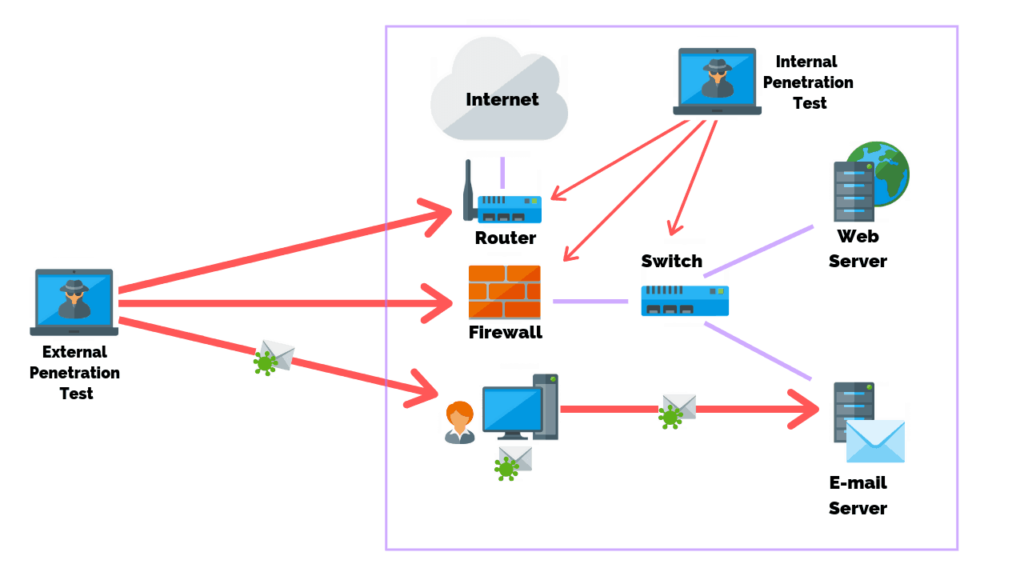
External testing
External penetration tests target the assets of a company that are visible on the internet, e.g., the web application itself, the company website, and email and domain name servers (DNS). The goal is to gain access and extract valuable data.
Internal testing
In an internal test, a tester with access to an application behind its firewall simulates an attack by a malicious insider. This isn’t necessarily simulating a rogue employee. A common starting scenario can be an employee whose credentials were stolen due to a phishing attack.
Blind testing
In a blind test, a tester is only given the name of the enterprise that’s being targeted. This gives security personnel a real-time look into how an actual application assault would take place.
Double-blind testing
In a double blind test, security personnel have no prior knowledge of the simulated attack. As in the real world, they won’t have any time to shore up their defenses before an attempted breach.
Targeted testing
In this scenario, both the tester and security personnel work together and keep each other appraised of their movements. This is a valuable training exercise that provides a security team with real-time feedback from a hacker’s point of view.
Penetration testing and web application firewalls
Penetration testing and WAFs are exclusive, yet mutually beneficial security measures.
For many kinds of pen testing (with the exception of blind and double blind tests), the tester is likely to use WAF data, such as logs, to locate and exploit an application’s weak spots.
In turn, WAF administrators can benefit from pen testing data. After a test is completed, WAF configurations can be updated to secure against the weak spots discovered in the test.
Finally, pen testing satisfies some of the compliance requirements for security auditing procedures, including PCI DSS and SOC 2. Certain standards, such as PCI-DSS 6.6, can be satisfied only through the use of a certified WAF. Doing so, however, doesn’t make pen testing any less useful due to its aforementioned benefits and ability to improve on WAF configurations.
What are the types of pen testing?
A comprehensive approach to pen testing is essential for optimal risk management. This entails testing all the areas in your environment.
Web apps. Testers examine the effectiveness of security controls and look for hidden vulnerabilities, attack patterns, and any other potential security gaps that can lead to a compromise of a web app.
Mobile apps. Using both automated and extended manual testing, testers look for vulnerabilities in application binaries running on the mobile device and the corresponding server-side functionality. Server-side vulnerabilities include session management, cryptographic issues, authentication and authorization issues, and other common web service vulnerabilities.
Networks. This testing identifies common to critical security vulnerabilities in an external network and systems. Experts employ a checklist that includes test cases for encrypted transport protocols, SSL certificate scoping issues, use of administrative services, and more.
Cloud. A cloud environment is significantly different than traditional on-premises environments. Typically, security responsibilities are shared between the organization using the environment and the cloud services provider. Because of this, cloud pen testing requires a set of specialized skills and experience to scrutinize the various aspects of the cloud, such as configurations, APIs, various databases, encryption, storage, and security controls.
Containers. Containers obtained from Docker often have vulnerabilities that can be exploited at scale. Misconfiguration is also a common risk associated with containers and their environment. Both of these risks can be uncovered with expert pen testing.
Embedded devices (IoT). Embedded / Internet of Things (IoT) devices such as medical devices, automobiles, in-home appliances, oil rig equipment, and watches have unique software testing requirements due to their longer life cycles, remote locations, power constraints, regulatory requirements, and more. Experts perform a thorough communication analysis along with a client/server analysis to identify defects that matter most to the relevant use case.
Mobile devices. Pen testers use both automated and manual analysis to find vulnerabilities in application binaries running on the mobile device and the corresponding server-side functionality. Vulnerabilities in application binaries can include authentication and authorization issues, client-side trust issues, misconfigured security controls, and cross-platform development framework issues.
Server-side vulnerabilities can include session management, cryptographic issues, authentication and authorization issues, and other common web service vulnerabilities.
APIs. Both automated and manual testing techniques are used to cover the OWASP API Security Top 10 list. Some of the security risks and vulnerabilities testers look for include broken object level authorization, user authentication, excessive data exposure, lack of resources / rate limiting, and more.
CI/CD pipeline. Modern DevSecOps practices integrate automated and intelligent code scanning tools into the CI/CD pipeline. In addition to static tools that find known vulnerabilities, automated pen testing tools can be integrated into the CI/CD pipeline to mimic what a hacker can do to compromise the security of an application.
Automated CI/CD pen testing can discover hidden vulnerabilities and attack patterns that go undetected with static code scanning.
Read More About NIST
Buy From Amazon
